End to End encryption with quarkus
This system architectural record is currently being refined.
Description of the problem
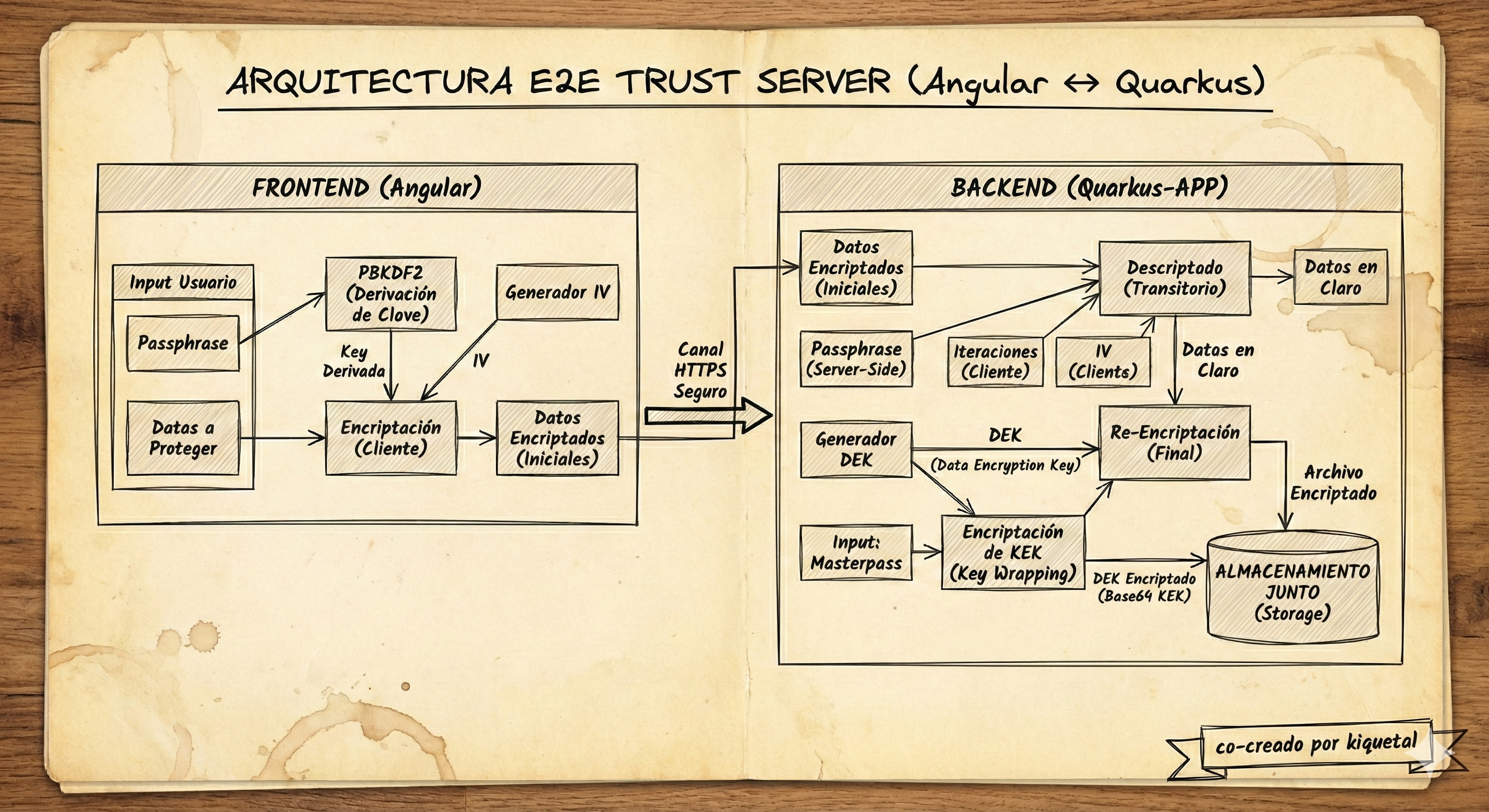
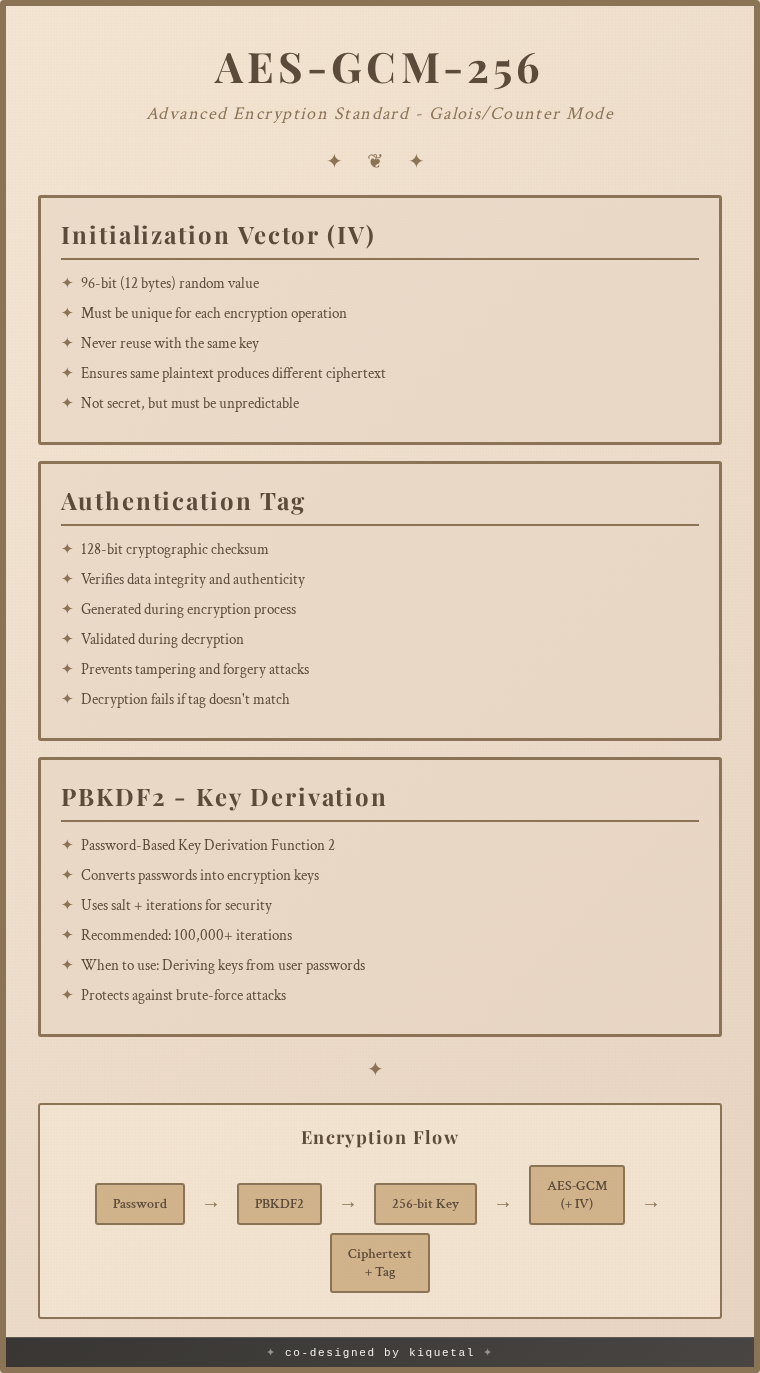
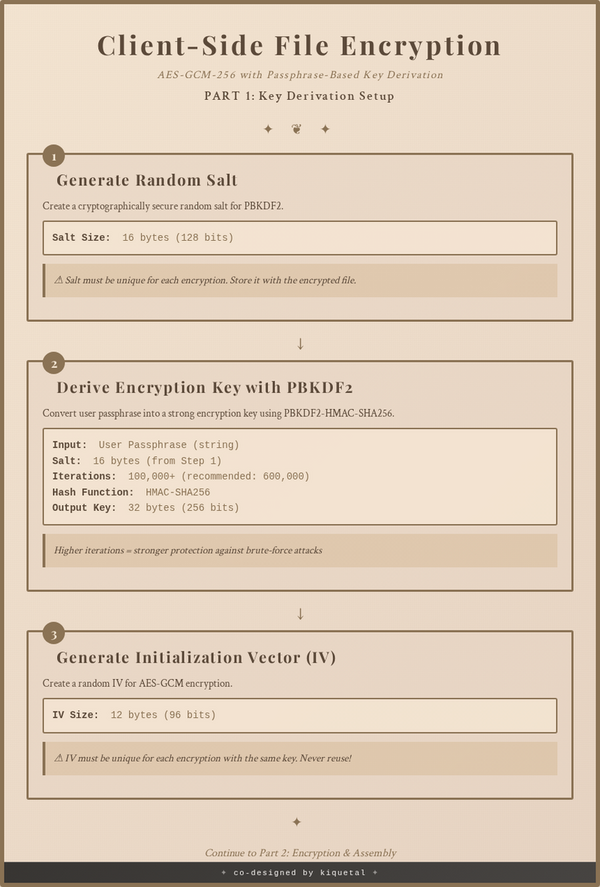
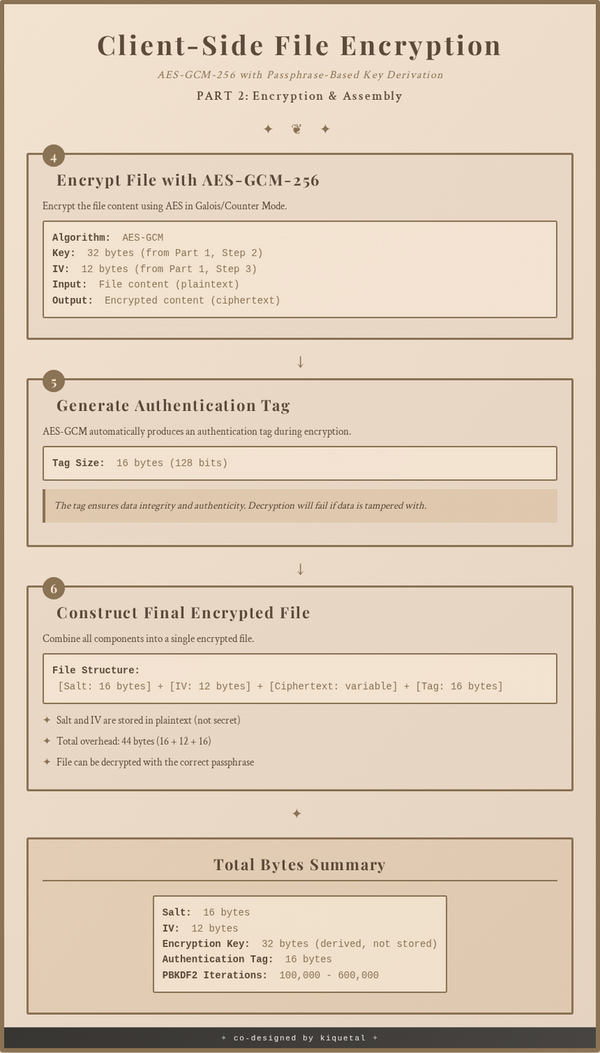
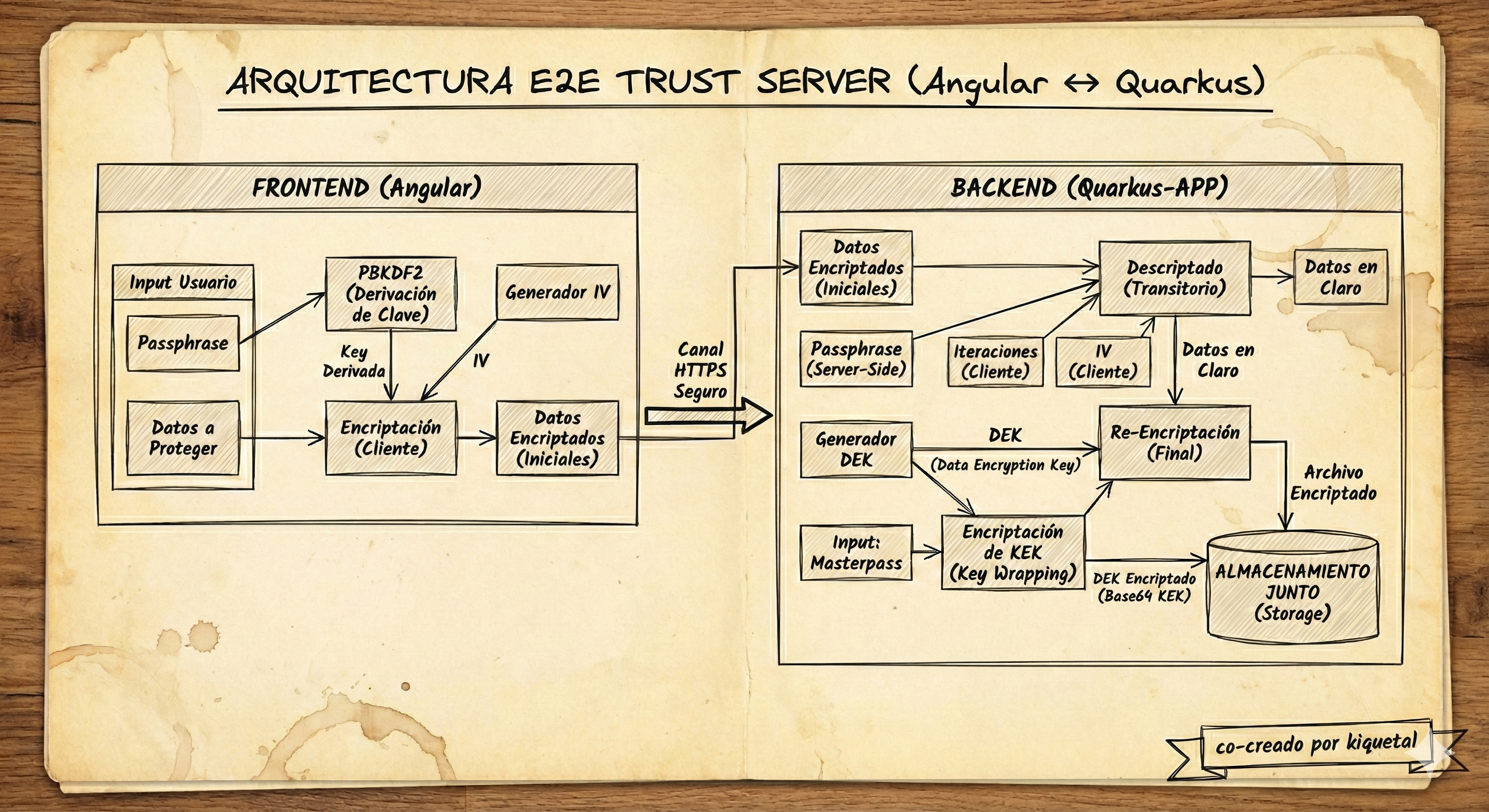
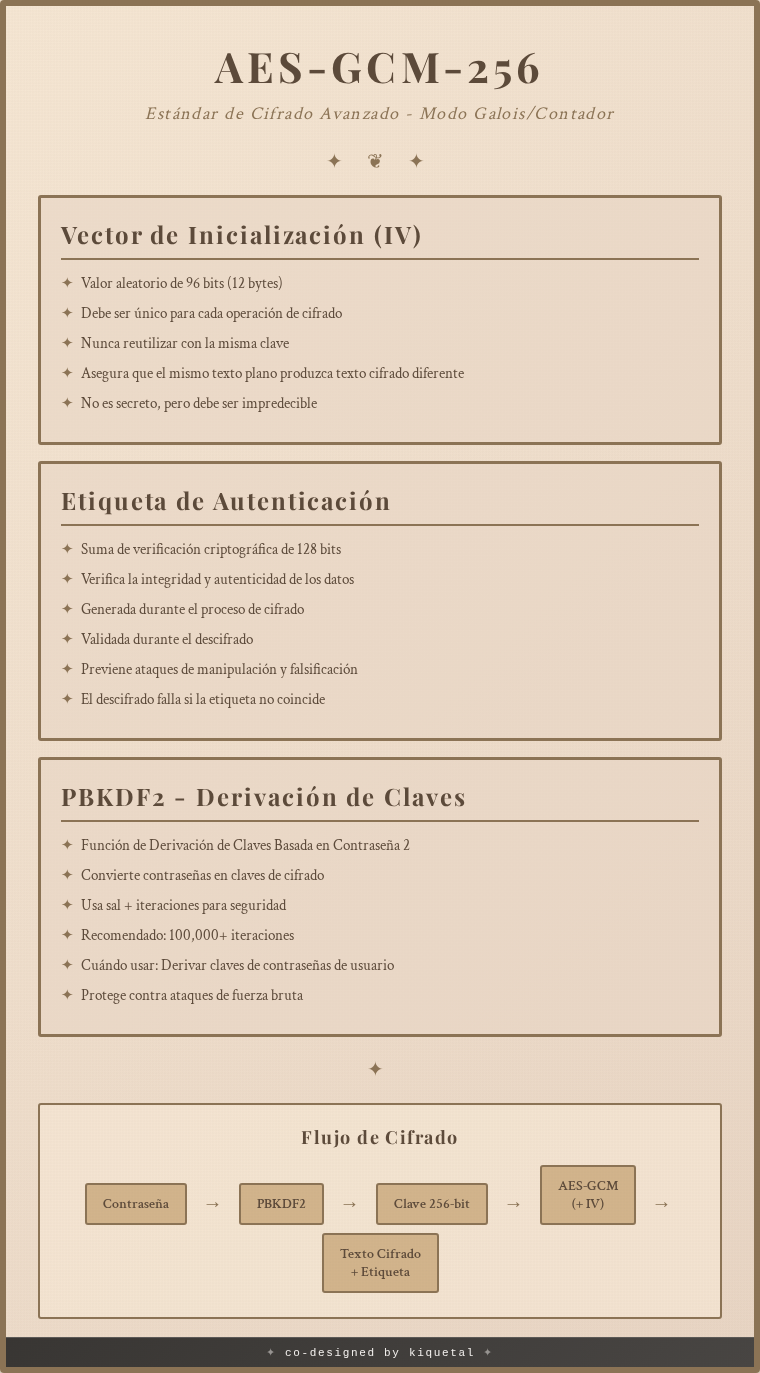
I wanted to implement encryption both in transit and at rest. For this particular scenario, I have implemented an Angular project that uses AES-256-GCM. The user enters a pre-defined passphrase that the server should share securely; using this passphrase, we start the process of encrypting a file. Following the AES-256 standard, we’ll end up with an encrypted file including an authentication tag.
We will use the same configuration from the client to decrypt on the server to ensure the file was correctly encrypted. Later, we will encrypt the file using a master key from the server. We’ll use envelope encryption to encrypt the randomly generated Data Encryption Key (DEK) used for the file and IV, and then encrypt this DEK with a Master Key (KEK). Using this pattern, we rely on the server to perform decryption operations.
Architecture
System Overview
┌──────────────────────────────────────────────────────────────────┐
│ User's Browser │
└──────────────────────────────────────────────────────────────────┘
│
│ 1. Access Web UI
│ https://e2equarks.kiquetal.dev/whisper
▼
┌──────────────────────────────────────────────────────────────────┐
│ Angular Frontend (SPA) │
│ ┌────────────────┐ ┌────────────────┐ ┌───────────────────┐ │
│ │ Passphrase │ │ Auth Guard │ │ MP3 Upload │ │
│ │ Component │ │ & Service │ │ Component │ │
│ └────────────────┘ └────────────────┘ └───────────────────┘ │
│ │ │ │
│ │ 2. Validate Passphrase │ │
│ │ (AES-GCM client-side encryption) │ │
│ └──────────────────┬───────────────────────┘ │
│ │ 3. Upload Encrypted File │
└────────────────────────────┼──────────────────────────────────────┘
│
│ Quinoa Integration
▼
┌──────────────────────────────────────────────────────────────────┐
│ Quarkus Backend │
│ ┌────────────────────────────────────────────────────────────┐ │
│ │ FileUploadResource │ │
│ │ • POST /api/validate-passphrase │ │
│ │ • POST /api/upload (100MB limit) │ │
│ └────────────────────────────────────────────────────────────┘ │
│ │ │
│ ┌────────────────────────────────────────────────────────────┐ │
│ │ CryptoService (service/) │ │
│ │ • Verify & decrypt from Angular │ │
│ │ • Encrypt with random DEK (streaming) │ │
│ │ • Create envelope (encrypt DEK with master key) │ │
│ └────────────────────────────────────────────────────────────┘ │
│ │ │
│ ┌────────────────────────────────────────────────────────────┐ │
│ │ S3StorageService (util/) │ │
│ │ • Generate S3 keys │ │
│ │ • Upload encrypted file │ │
│ │ • Upload envelope metadata │ │
│ └────────────────────────────────────────────────────────────┘ │
│ │ │
│ │ 4. Store Encrypted Data │
└────────────────────────────┼──────────────────────────────────────┘
│
│ S3 Client
▼
┌──────────────────────────────────────────────────────────────────┐
│ S3/Tigris Object Storage │
│ • uploads/{email}/{uuid}/file.enc (encrypted data) │
│ • uploads/{email}/{uuid}/metadata.json (encrypted DEK) │
│ │
│ Dev: LocalStack (Docker container) │
│ Prod: Tigris or AWS S3 │
└──────────────────────────────────────────────────────────────────┘
Encryption Flow
User Browser
↓ (Client encrypts with passphrase: AES-256-GCM + PBKDF2)
Encrypted File → Quarkus Backend
↓ (Verify passphrase & decrypt: streaming)
Plaintext Data → CryptoService
↓ (Encrypt with random DEK: streaming)
DEK-Encrypted Data
↓ (Encrypt DEK with master key: envelope)
S3/Tigris Storage
├─ Encrypted File Data
└─ Metadata (with encrypted DEK)